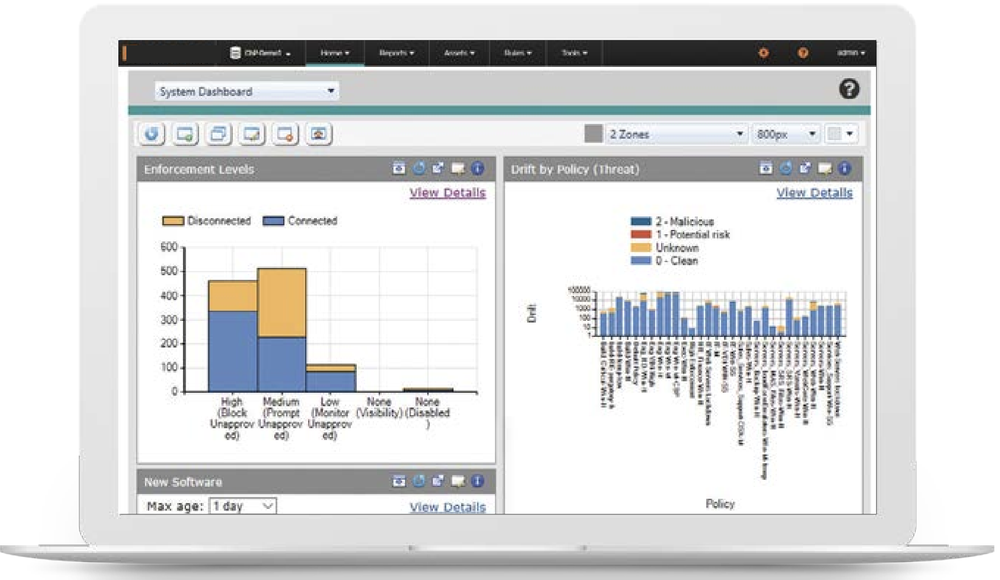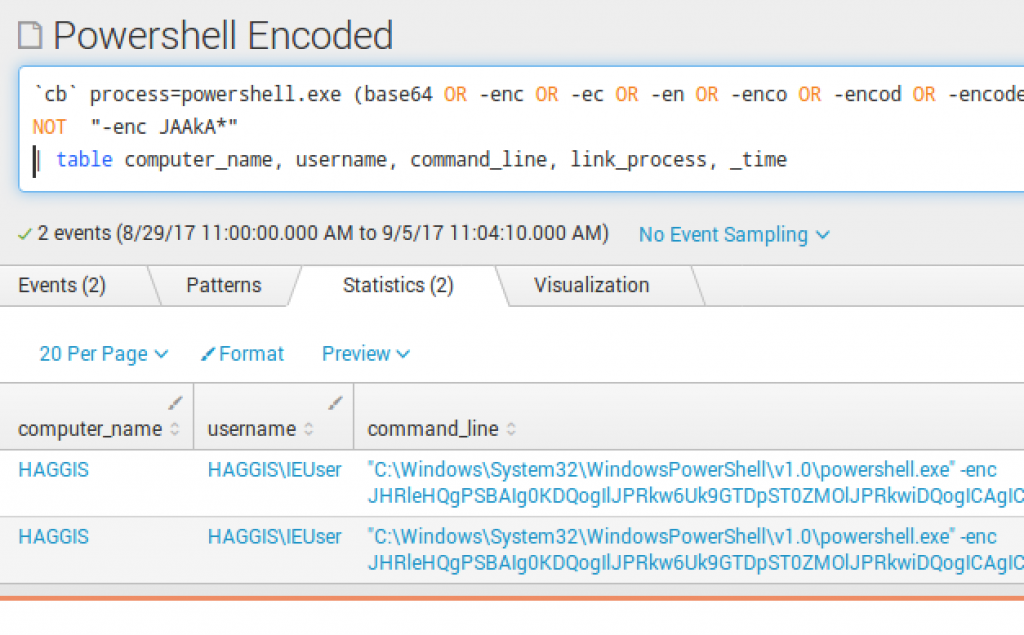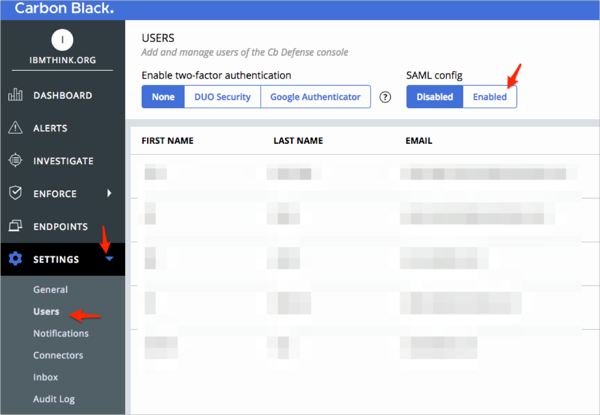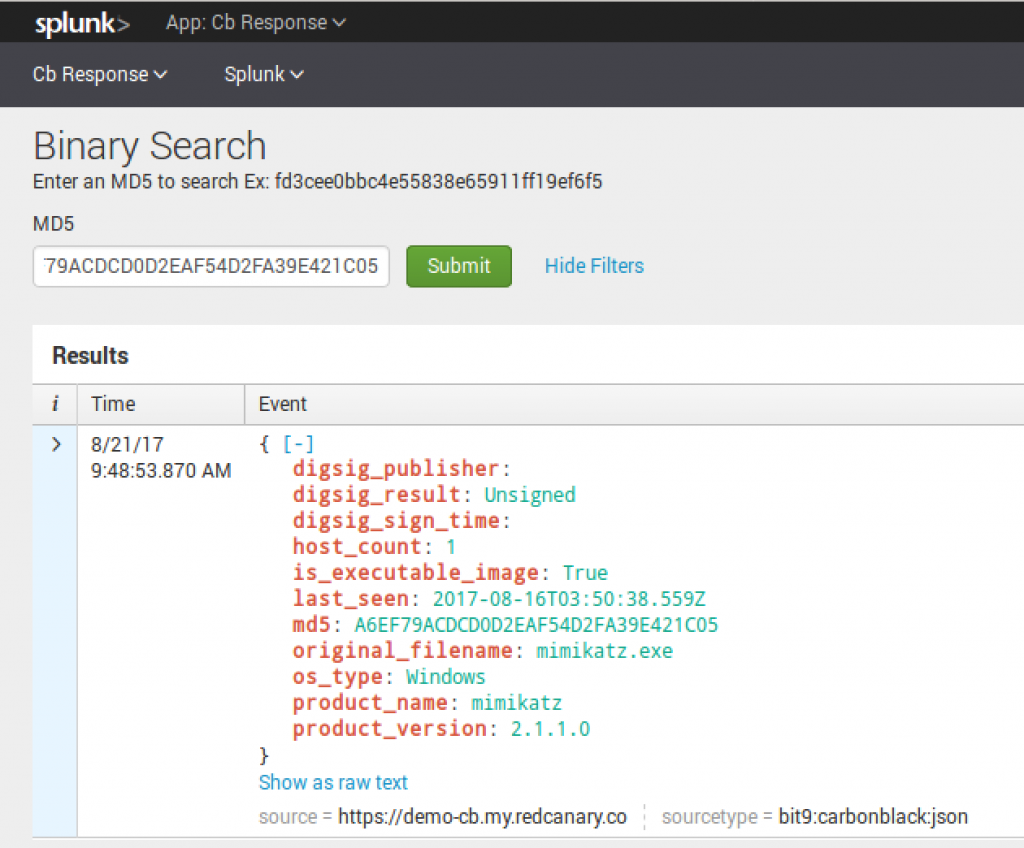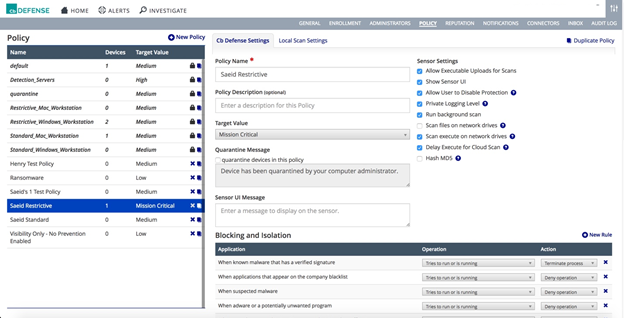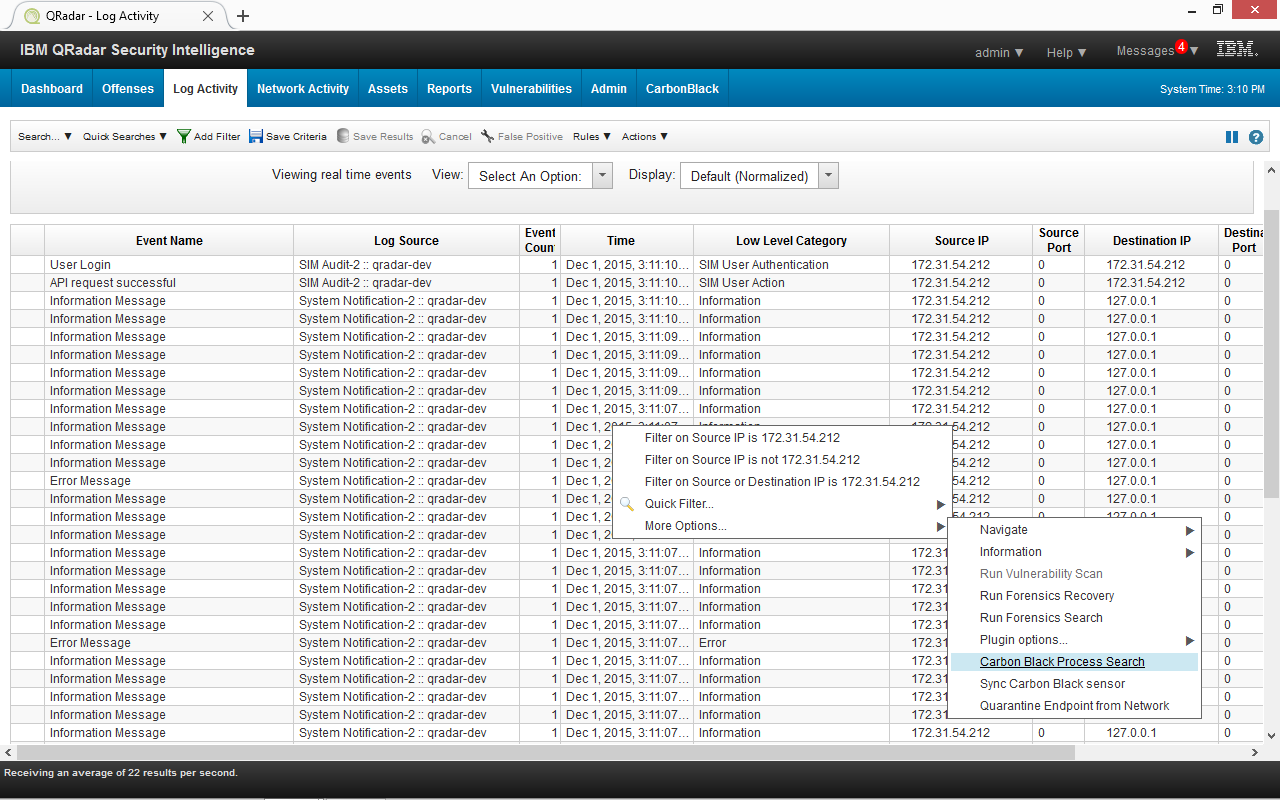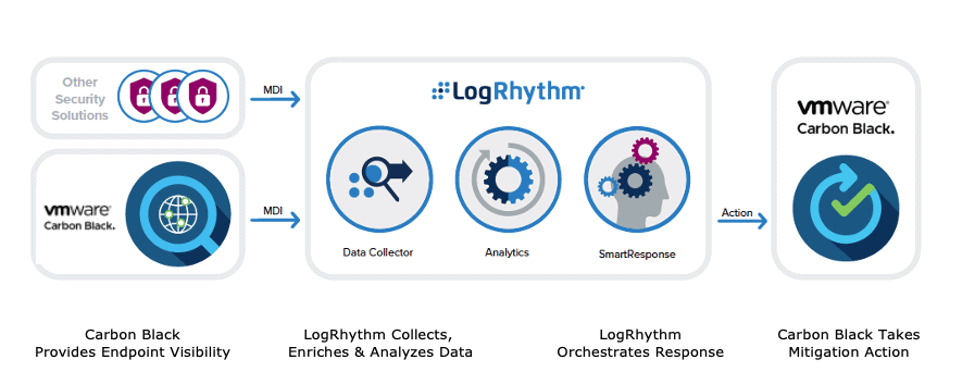
Analyze Attacker Behavior, Endpoint Detection Anomalies with LogRhythm and Carbon Black - Security Boulevard

Schematic of log conductivity versus carbon black content describing a... | Download Scientific Diagram
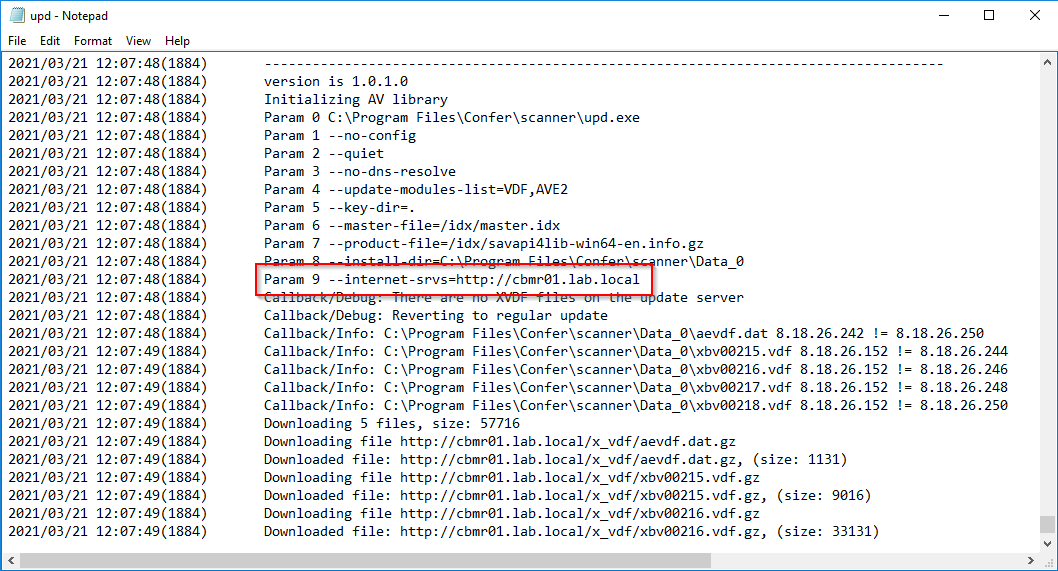
VMware Carbon Black Endpoint Detection and Response (EDR) Windows Sensor 7.2 Supplemental Administrative Guidance for Common Cri